
Colorado became the third state in the US to pass comprehensive privacy legislation when Governor Jared Polis signed into law the Colorado Privacy Act (CPA) on July 8, 2021. This law will go into effect July 1, 2023 and give Colorado residents the rights to access, correct, and delete any personal data businesses have collected on them as well as the rights to obtain a readily usable copy of that data and to opt out of having their personal data processed.
Many similarities exist between Colorado’s privacy law and the laws already enacted in California and Virginia; however, each state’s law has its own unique nuances that require businesses to pay close attention to ensure compliance. As with other privacy laws in the US and around the world, compliance with Colorado’s new legislation will be critical for organizations, as failure to do so can carry a hefty fine — up to $20,000 per violation in Colorado.
Reduce your team’s routine work and help them focus on what inspires them.
Stop using spreadsheets, documents, and unwieldy ticketing systems for your incident readiness and response efforts.
Who Must Comply with CPA
CPA follows the trend of other global privacy laws by having an extra-territorial scope. This means that organizations located outside of Colorado must still comply with the law if they collect and process data on Colorado residents.
Specifically, CPA applies to any organization that (1) conducts business in Colorado or intentionally targets Colorado residents with commercial products or services and (2) meets one of the following requirements:
- Controls or processes personal data of at least 100,000 consumers during a calendar year
- Drives revenue or receives a discount on goods or services from selling personal data and processes or controls personal data of at least 25,000 consumers
CPA is somewhat unique in that the minimum requirements it sets are based on the extent of consumer data a business processes rather than revenue.
Importantly, there are a few cases where businesses are exempt even if they pass those thresholds. CPA notes the following exemptions:
- Employee data: CPA only applies to Colorado residents acting in an “individual or household context” and notes that anyone acting in a “commercial or employment context” (e.g. as a job applicant) is not covered under the law. This means businesses do not need to consider internal employee data when it comes to CPA compliance.
- Certain instances of selling data: CPA allows for certain instances of selling data, including sharing data with processors or affiliates, disclosing data to third parties to deliver a product or service requested by the consumer, sharing data as part of a merger, acquisition, or bankruptcy transaction, and disclosing data intentionally made public by the consumer (e.g. through a mass media channel).
- Organizations subject to Gramm-Leach-Bliley Act: Any organization subject to the federal Gramm-Leach-Bliley Act is exempt from CPA. However, other organizations that typically receive similar exemptions, such as non-profits and those subject to the Health Insurance Portability and Accountability Act (HIPAA), must still adhere to CPA if they meet the minimum requirements.
How CPA Gets Enforced
Enforcement responsibilities for CPA sit with both the Colorado Attorney General and state district attorneys. Once the law goes into effect in 2023, either the attorney general or district attorneys can begin the enforcement process by issuing a notice to any companies they find in violation of the law.
Once the notice gets issued, the organization will have 60 days to cure the violation before the attorney general or district attorney takes action. However, this right to cure will only exist for the first two years that the law is in place. Starting January 2025, organizations will not have the right to cure any violations before enforcement action.
If the organization fails to cure the violation (or if any violation occurs after the right to cure goes away in 2025), the attorney general and district attorneys can issue a fine of up to $20,000 per violation. CPA does not outline this penalty though. Rather, it comes from an older law, the Colorado Consumer Protection Act, since any instance of non-compliance with CPA is considered a deceptive trade practice under that 2016 law.
Incident Response Measures Required Under CPA
CPA puts the responsibility on organizations to properly secure any data they collect about consumers, noting that security protocols should be “appropriate to the volume, scope, and nature of the personal data processed.”
Any organization that fails to meet this responsibility and experiences a data privacy incident must go into response mode and issue an appropriate notification. While CPA does not outline anything in regard to incident response, an older law, C.R.S. § 6-1-716, dictates strict security breach notification requirements for the state.
Under Colorado law, once an organization becomes aware of a potential security breach, they must investigate the issue to understand any impact to personal information they have on consumers. Personal information is defined as:
- Social security numbers
- Student, military, or passport ID numbers
- Drivers license or identification card numbers
- Medical information
- Health insurance identification number
- Biometric data
- Username or email address in combination with a password or security question and answer
- Account number or credit card number in combination with any required security code
If the investigation confirms an incident has occurred that exposed personal information, businesses must issue a notice about the incident within 30 days (noting that some delays are allowed in coordination with law enforcement). The notice should go to all affected Colorado residents in either written, telephone, or electronic form and must include the following information:
- Date, estimated date, or estimated date range of the breach
- Description of the personal information compromised in the breach
- Information to contact the organization with any questions about the breach
- A note that customers can get information from the Federal Trade Commission (FTC) and credit reporting agencies about fraud alerts and security freezes, plus toll-free numbers, addresses, and websites to contact those agencies
Additionally, if the incident compromised Colorado residents’ username or email address in combination with a password or security questions and answers, organizations must direct them to protect their accounts. For example, this direction might include instructions to change their password or security questions and answers.
If the incident affected more than 500 Colorado residents, the organization must also notify the State Attorney General via email within the same 30 day window. This notice should include:
- Organization name and a primary contact
- Date the organization learned there may have been a security breach
- Date the organization determined a security breach occurred
- Date the organization notified affected Colorado residents
- Number of Colorado residents affected by the breach
- Total number of individuals affected by the breach
- Copy of the notice provided to Colorado residents
If the incident affected more than 1,000 Colorado residents, the organization must also notify national consumer reporting agencies and share the date on which the affected consumers will be notified and the approximate number of people who will receive the notification.
Finally, the state does allow for a substitute notice if the cost of providing a notice will exceed $250,000, if the number of Colorado residents affected is more than 250,000, or if the organization doesn’t have sufficient contact information to provide notice. In these cases, organizations can:
- Notify affected individuals via email, if they have the appropriate contact information
- Post a notice conspicuously on their website
- Share a notification with major statewide media outlets
Types of Privacy Incidents that Require Notification Under CPA
Numerous situations can create a privacy incident that requires notification under CPA. This covers everything from a cyber attack that exposes encrypted personal information to improper usage or accidental loss by organizations. Examples of commonly encountered incidents that will trigger a response include:
Watering Hole Attack
Watering hole attacks are a type of social engineering cyber attack in which a hacker profiles its target victim (such as a specific user or group of employees at an organization), identifies websites they are likely to visit, and then infects one or more of those websites to gain access to the victims’ computers and/or network. These types of attacks are particularly dangerous because they give third parties access to secured information in a way that is highly difficult to detect. Additionally, hackers often use a watering hole attack as a way to gain access to more secure organizations by preying on individual employee behaviors.
Mistakenly Exposed Data
Mistakenly sharing information on an improper channel or sending data to the wrong recipient can expose personal details about consumers to third parties and therefore requires incident response. Common examples of mistakenly exposed data include sharing private information over an unencrypted channel like email or accidentally responding to a consumer’s request for information with details about someone else instead. Even if these are innocent mistakes, they still require a notification under CPA since these situations expose private data and can lead to serious risks for the consumers involved.
Improperly Processed or Sold Data
An organization that continues to process or sell data after consumers have opted out (a right granted to them under CPA) creates a privacy incident that requires notification. The situation remains the same regardless of whether the activities happened by accident or on purpose. In either case, the organization failed to comply with consumers exercising their right to opt out of data-related activities and therefore qualifies as a breach.
How Organizations Can Prepare for CPA
Although CPA assigns a duty of care to organizations that collect and process consumer data, even the most secure organizations are likely to experience an incident at some point or another. Recognizing this reality and proactively preparing for incident response accordingly can help organizations respond faster to reduce costs and speed recovery when an issue arises.
To start, this preparation should include:
- Establishing visibility into how data gets collected and used to help identify if something goes wrong
- Assigning a person or a team to be responsible for security protocols and incident response
- Developing a clear incident response plan that can be put into action at any time
Diving deeper, organizations need to consider three critical phases of incident response:
1) Readiness
Given that Colorado requires organizations to notify consumers about an incident within 30 days and offers a cure period of 60 days to start, it’s essential for companies to have a plan in place before they ever need it. Having this plan in place will enable teams to completely and confidently respond within the necessary timeframe, and it can even help lower costs.
During the readiness phase, organizations should:
- Take the time to review the requirements set forth in regulations like CPA as well as any contracts with customers and partners
- Outline clear incident response plans according to each of those guidelines
- Regularly revisit regulations and contracts to capture any changes and adjust response plans accordingly
2) Response
Having a response plan already in place allows organizations to jump into action immediately when an incident occurs. Of course knowing how to respond when an incident occurs is one thing; being able to identify when a response is needed and what happened to trigger this response is another. Colorado requires organizations to determine these issues and evaluate the fallout, making this type of complete response essential.
During the response phase, organizations should:
- Have clear visibility to determine what happened, when it happened, the data and consumers involved, and any potential risks
- Issue the proper notifications based on regulatory and contract requirements as laid out during the readiness phase
- Consider remediation options to patch the problem and prevent similar issues going forward
3) Ongoing Management
Incident response can not be a one-and-done exercise. Regulations like CPA will evolve often and new ones will continue to pop up. Additionally, contracts with customers and partners will change and new types of threats to data security will come about. All of these situations mean that organizations must regularly revisit incident response measures to maintain a proactive stance.
During the ongoing management phase, organizations should:
- Introduce a centralized dashboard as a single source of truth for monitoring and reporting
- Add response plans and updates to any regulations and contracts to that dashboard
- Make that dashboard accessible to all stakeholders for long-term alignment and visibility
Comparing US Privacy Laws: Side-by-Side Breakdown of Colorado, Virginia, and California Regulations
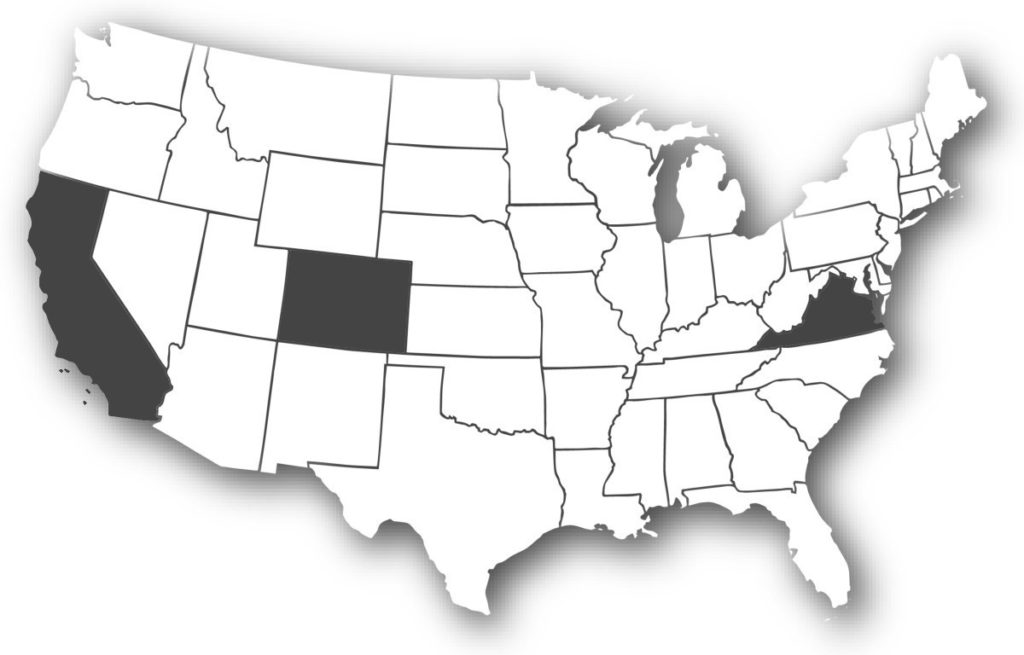
Passing the CPA in July 2021 made Colorado the third US state to enact comprehensive privacy legislation, alongside Virginia and California. While a lot of similarities exist between the laws in these three states, each one has its own nuances that are important for businesses to understand as they aim for compliance across the board. With that in mind, here’s a side-by-side breakdown comparing the privacy laws in each state.
| Colorado – CPA | Virginia – CDPA | California – CCPA & CPRA | |
|---|---|---|---|
| Effective date | July 1, 2023 | January 1, 2023 |
|
| Rights granted |
|
|
|
| Enforcement | State Attorney General and District Attorneys | State Attorney General |
|
| Penalty for non-compliance | Up to $20,000 per incident | Up to $7,500 per incident |
|
| Notification timeline | Within 30 days of awareness that an incident occurred | “Without unreasonable delay” once an incident is identified | “Without unreasonable delay” once an incident is identified |
Prioritizing Proactive Incident Response
Colorado is the most recent state to enact comprehensive privacy legislation, and it certainly won’t be the last. In the coming months and years, even more states and countries will follow suit, and we are also likely to see evolutions to recently passed regulations like CPA.
Keeping track of these many regulations and the nuances of each one will be critical for organizations to not only remain compliant, but also mitigate any costs and fallout if and when an incident does occur.
Achieving this goal requires organizations to prioritize proactive incident response by keeping track of regulations, putting response plans in place, assigning responsibility, and regularly revisiting all of those measures as regulations and organizational policies change. Importantly, this type of proactive incident response will help organizations approach any issues that do arise quickly and confidently, which can help reduce recovery time and costs.
Tired of paying for spreadsheets of regulations that require close review and manual effort?
Get your data breach response plan into an actionable form using the BreachRx platform in a matter of days!